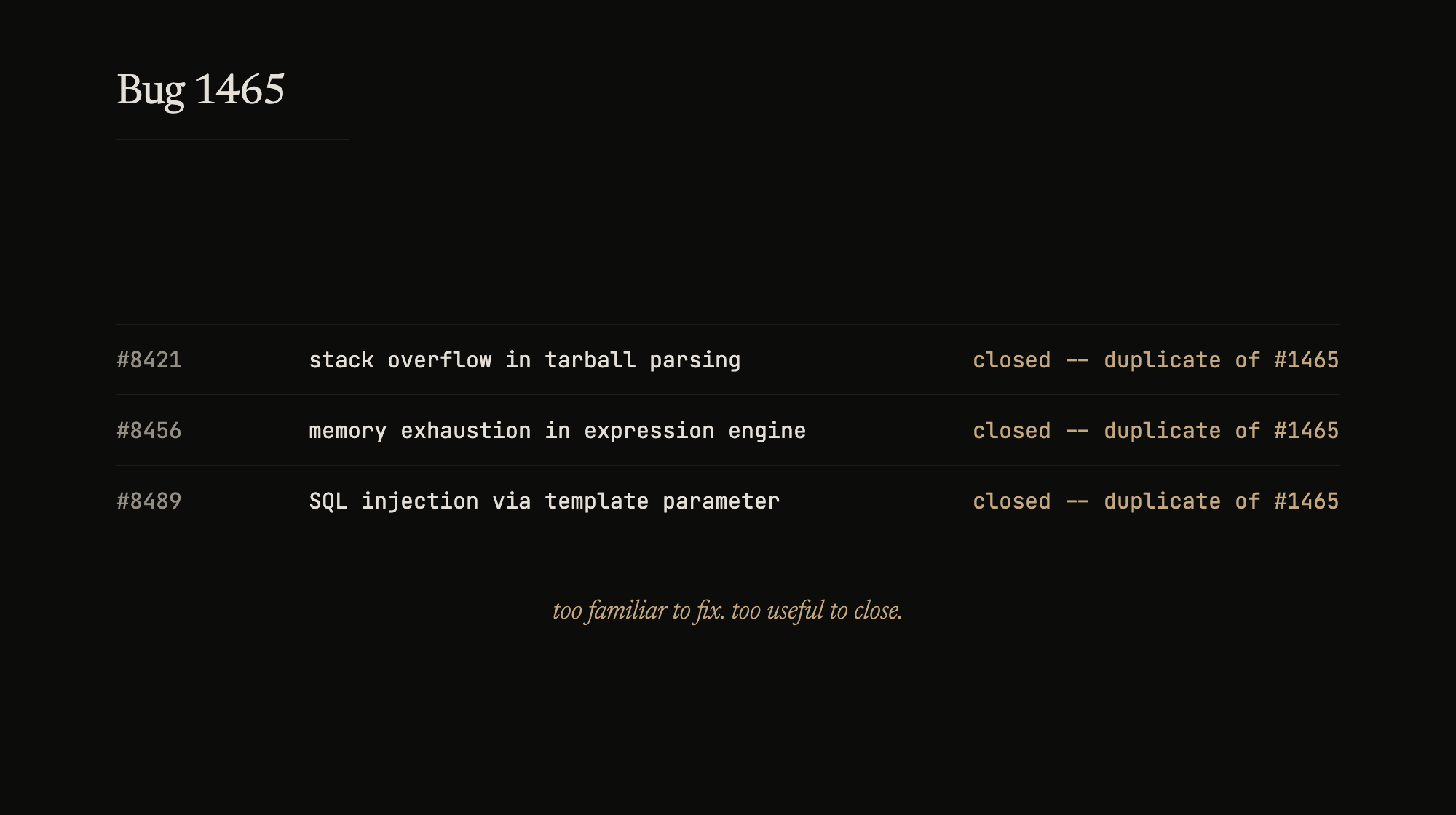
Three bugs walk into a triage queue.
A stack overflow. Symlink loop in tarball parsing, unbounded recursion, process crashes. Build a PoC, trace the call chain, write the report.
“Duplicate of #1465”
Memory exhaustion. String replace in an expression engine, exponential allocation, no cost limit. Different repo, different CWE, different everything. PoC, trace, report.
“Duplicate of #1465”
SQL injection. Template parameter escaping that wraps but doesn’t escape. Different repo again. PoC, trace, report.
“Duplicate of #1465”
I looked up #1465. Low number. Filed before half the code it covers existed. The fix PR has been open for a month. The bug outlived two refactors, a major version bump, and a dozen rediscoveries.
At some point you stop being frustrated and start being impressed. Not at the triage – at the bug.
Every triage queue has one. The canonical number that was there before the team, before the intern who filed it moved on. Researchers stumble into it now and then, build gold evidence for something already known. Triagers keep it open like a pet – too familiar to fix, too useful to close.
That’s not a vulnerability. That’s a load-bearing bug. #1465 is doing its job.